Decryption off/on – a 1 hour snapshot
16 March
In a recent engagement ANSecurity enabled outbound decryption from Windows end-user devices to the Internet and internal services, with decryption enabled the firewall is able to utilise it’s licenced features to detect and prevent a range of threats, including:
-
Known malware – prevent it early at the network level from reaching devices with an extra layer of protection on top of your existing endpoint anti-malware services.
-
Vulnerability exploits – patching of software (of particular note operating systems, office applications, and web browsers) doesn’t always move as fast as administrators would like, network firewalls have a range of measures to prevent exploits at the network level.
-
URL filtering – don’t just filter the domain, filter the full URL to allow access to only authorised services, particularly critical on websites (such as GitHub) that allow user generated content to be uploaded – one half of the website could be useful while the other half is very malicious.
-
GenAI monitoring – write granular policies on which GenAI tools can/can’t be used and what features of those tools are permitted (e.g. block file uploads).
-
Phishing prevention – detect and prevent the submission of usernames/passwords to unauthorised websites to cut off phishing attacks early.
-
Unknown malware – it’s trivial for threat actors to generate malware with never before seen signatures, the sandboxing services provided by firewalls allow the detailed examination of never before seen files and informs administrators if a newly discovered malware is seen.
The example below from the overview tab on a Palo Alto Networks firewall shows the difference with and without decryption for end-user devices over a one hour period between two days, previously a significant proportion of the traffic was encrypted and effectively blinded the firewall, once enabled the firewall has near complete visibility into what is passing through it and now provides significant return on investment with those licences.

Without decryption, although application identification can ‘identify’ many applications there is no ability to inspect the payloads of network.
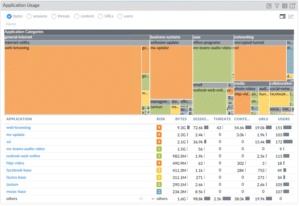
With Decryption – note that the ‘ssl’ category has significantly dropped, the firewall can now perform detailed inspection of all payloads.